The Best Traffic Bot and Website Automation Software




Earn money by clicking ads
on your website or beat
your competitors by
clicking their AD
automatically.
Join popular freelancing
platforms like Fiverr, Seo
Clerks and start selling
website traffic there and
make some money!
: Only download WinRAR or 7-Zip from their official sites.
A (Roshal Archive) is a compressed data container that holds one or more files in a smaller, more manageable package [ 1.3.1 , 1.3.8 ]. These files are used to save storage space and speed up transfers across the internet [ 1.3.10 , 1.3.14 ]. Essential Safety First
What are you expecting to find inside this archive?
: Be wary if the archive contains files ending in .exe , .msi , or .bat , as these can execute code on your system [1.4.2]. How to Open the Archive
If you’ve recently encountered a download for , you might be wondering what this file is and how to handle it safely. Compressed archives like this are common for sharing large datasets or multiple files, but they also require specific tools and safety precautions. What is a .RAR File?
: You can upload the file or paste its download URL into VirusTotal to check it against dozens of antivirus engines simultaneously [ 1.4.1 ].
Before you extract any unknown file like z644id9gev78.rar , it is critical to verify its safety:
Select to unpack the contents in your current folder, or "Extract to [Folder Name]" to keep things organized [ 1.2.1 , 1.3.5 ]. Summary Checklist Verify the source : Did you expect this file? Run a virus scan : Use Microsoft Defender or VirusTotal.
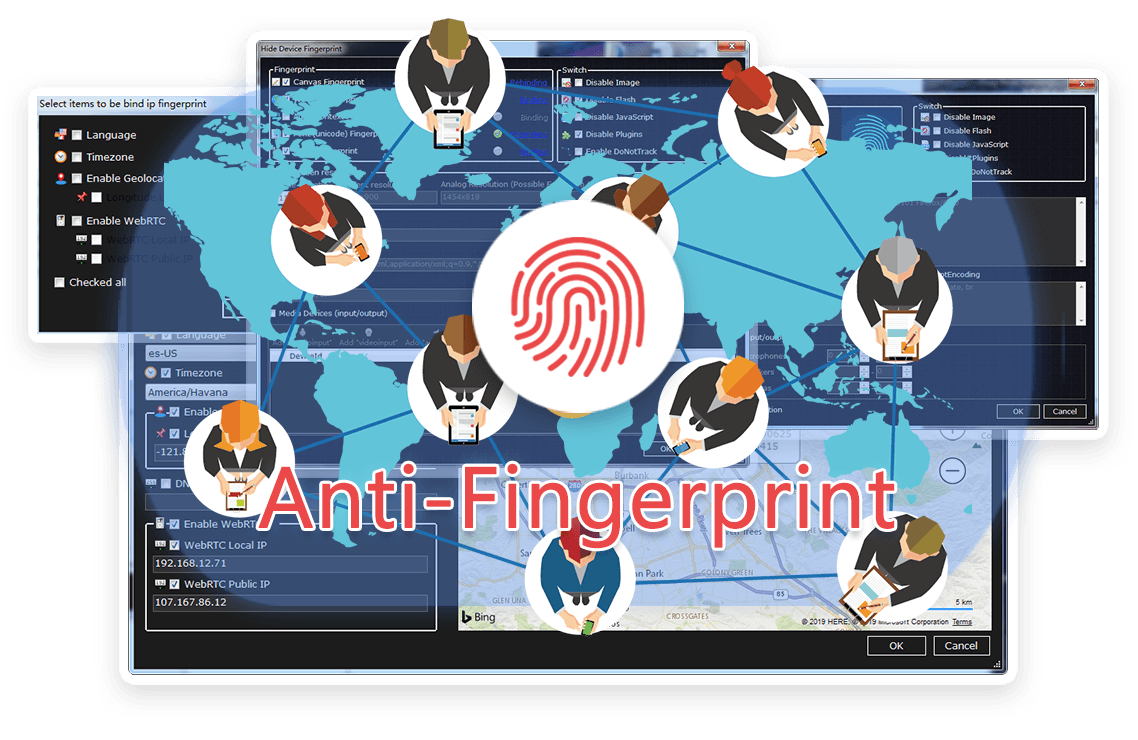
TrafficBotPro is a software web automation software that allows you to hide and control your digital
fingerprint by spoofing all parameters that websites can see. By masking these settings, you can bypass
anti-fraud systems by impersonating your real internet identity.
It helps you create a large number of profiles, each with its own digital fingerprint. These profiles do not
overlap with each other, so the website cannot ban your account. This is useful for performing various tasks
on the Internet.
Our software approaches browser fingerprinting in a completely indigenous way. Instead of trying to prevent websites from reading your computer’s fingerprint, our software allows reading it but replaces your original fingerprint with a different one. When you use a proxy IP, our software is fully different to other software that only add a proxy to your browser to work, our software will set the timezone, language, DNS and location etc... is matched to your proxy IP, that will make you looks like a real people from the proxy IP. Our software can also generate different device fingerprint and bind different fingerprint with your accounts. Once the account is bind with proxy IP, device fingerprint and other settings, the account will use these settings all the time with all operation. That is why you can use our software to mange and operate many accounts with different proxy safely.




: Only download WinRAR or 7-Zip from their official sites.
A (Roshal Archive) is a compressed data container that holds one or more files in a smaller, more manageable package [ 1.3.1 , 1.3.8 ]. These files are used to save storage space and speed up transfers across the internet [ 1.3.10 , 1.3.14 ]. Essential Safety First
What are you expecting to find inside this archive?
: Be wary if the archive contains files ending in .exe , .msi , or .bat , as these can execute code on your system [1.4.2]. How to Open the Archive
If you’ve recently encountered a download for , you might be wondering what this file is and how to handle it safely. Compressed archives like this are common for sharing large datasets or multiple files, but they also require specific tools and safety precautions. What is a .RAR File?
: You can upload the file or paste its download URL into VirusTotal to check it against dozens of antivirus engines simultaneously [ 1.4.1 ].
Before you extract any unknown file like z644id9gev78.rar , it is critical to verify its safety:
Select to unpack the contents in your current folder, or "Extract to [Folder Name]" to keep things organized [ 1.2.1 , 1.3.5 ]. Summary Checklist Verify the source : Did you expect this file? Run a virus scan : Use Microsoft Defender or VirusTotal.
Browse the latest blog posts for in-depth insights into anti-detection and online privacy. Stay up-to-date!


Submit your need here, we will check and give you reply asap.
