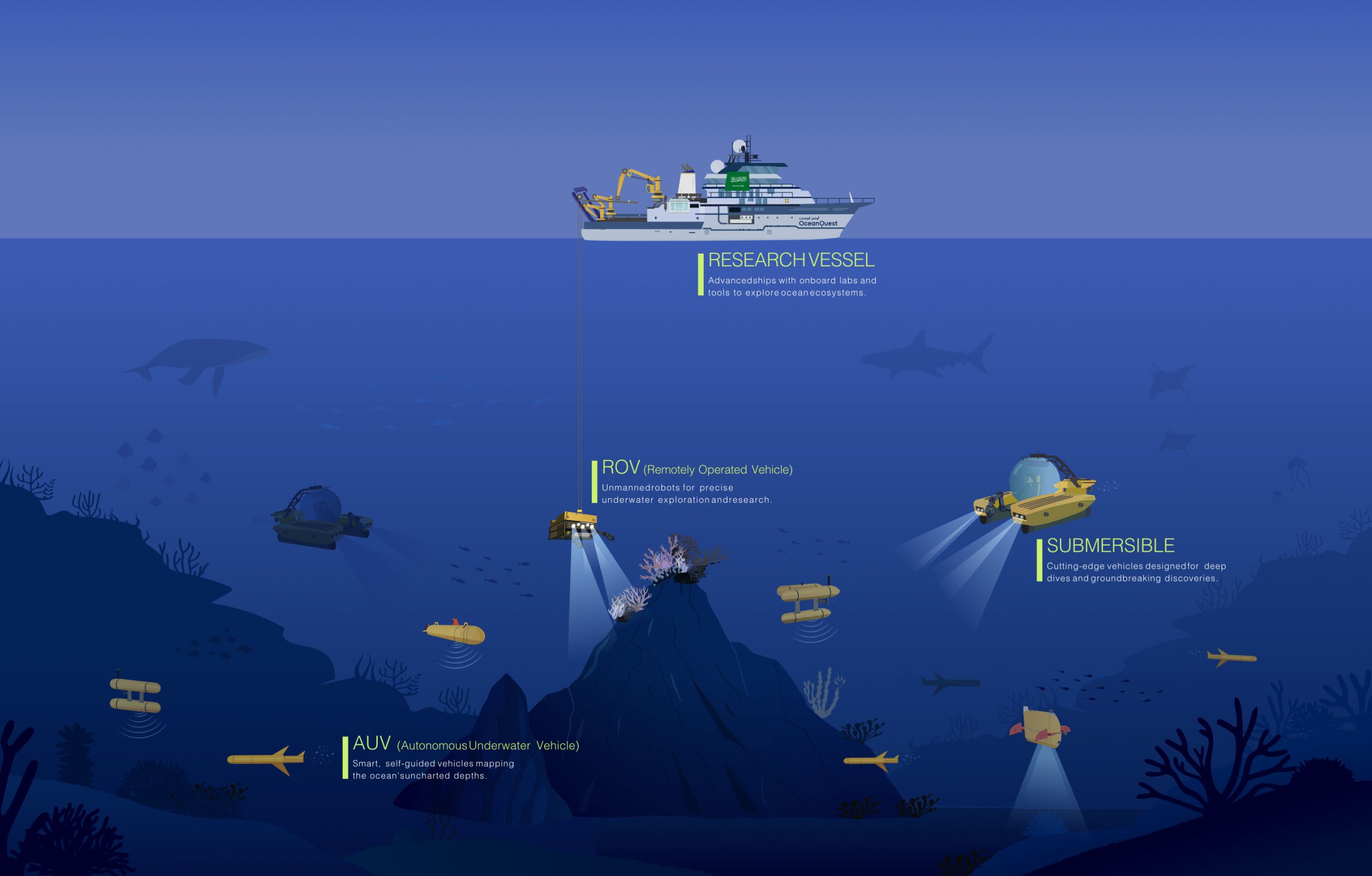
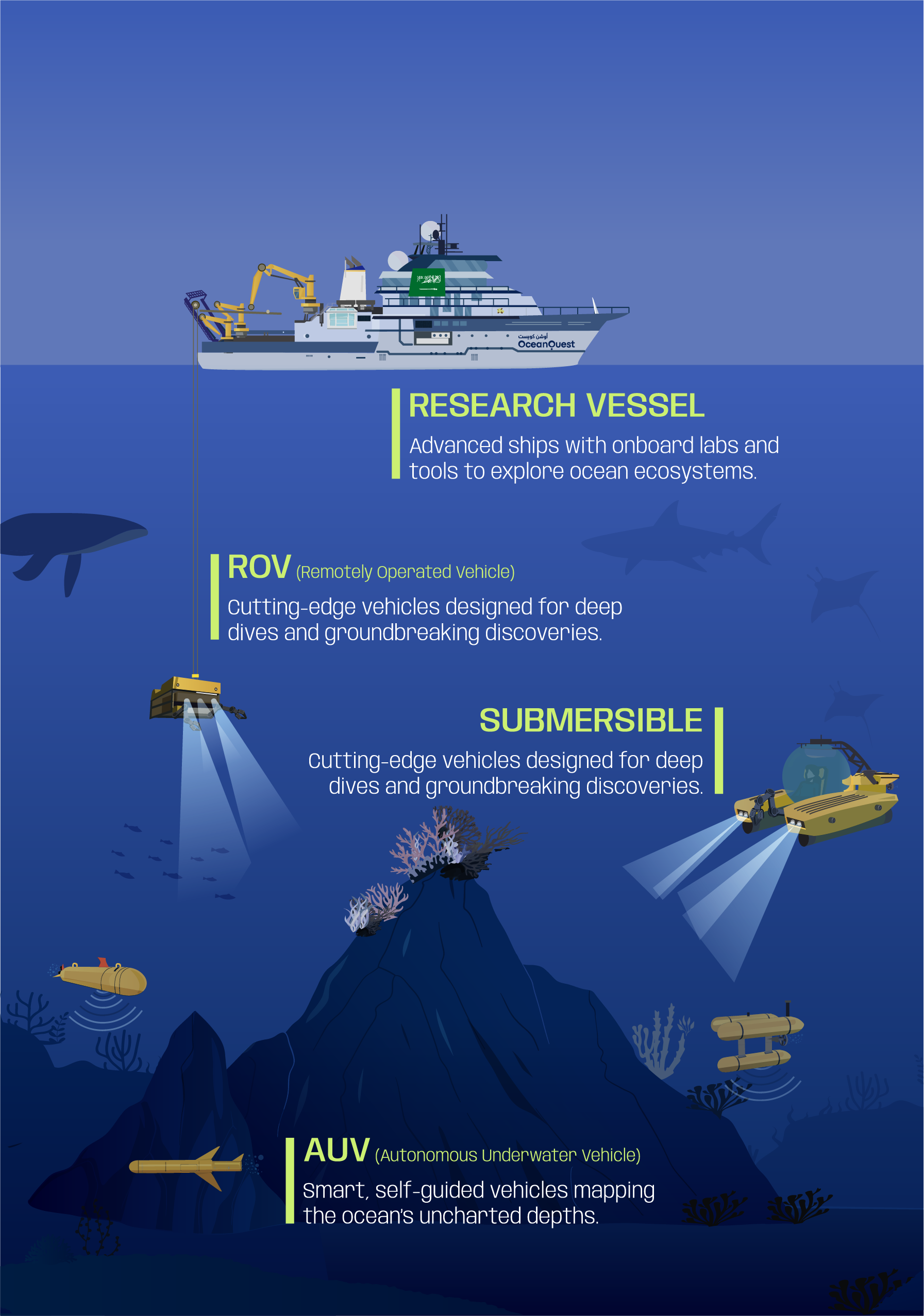
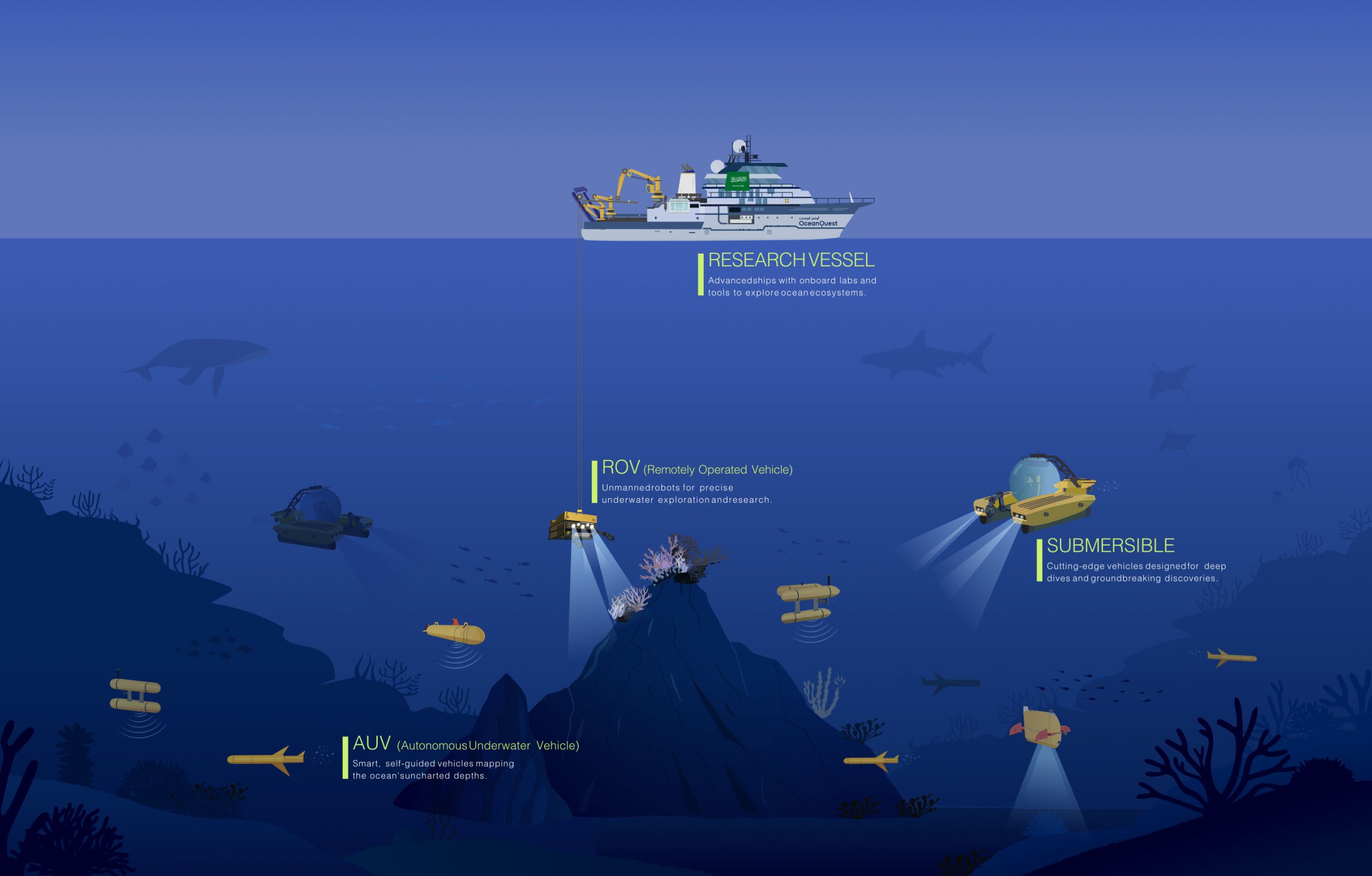
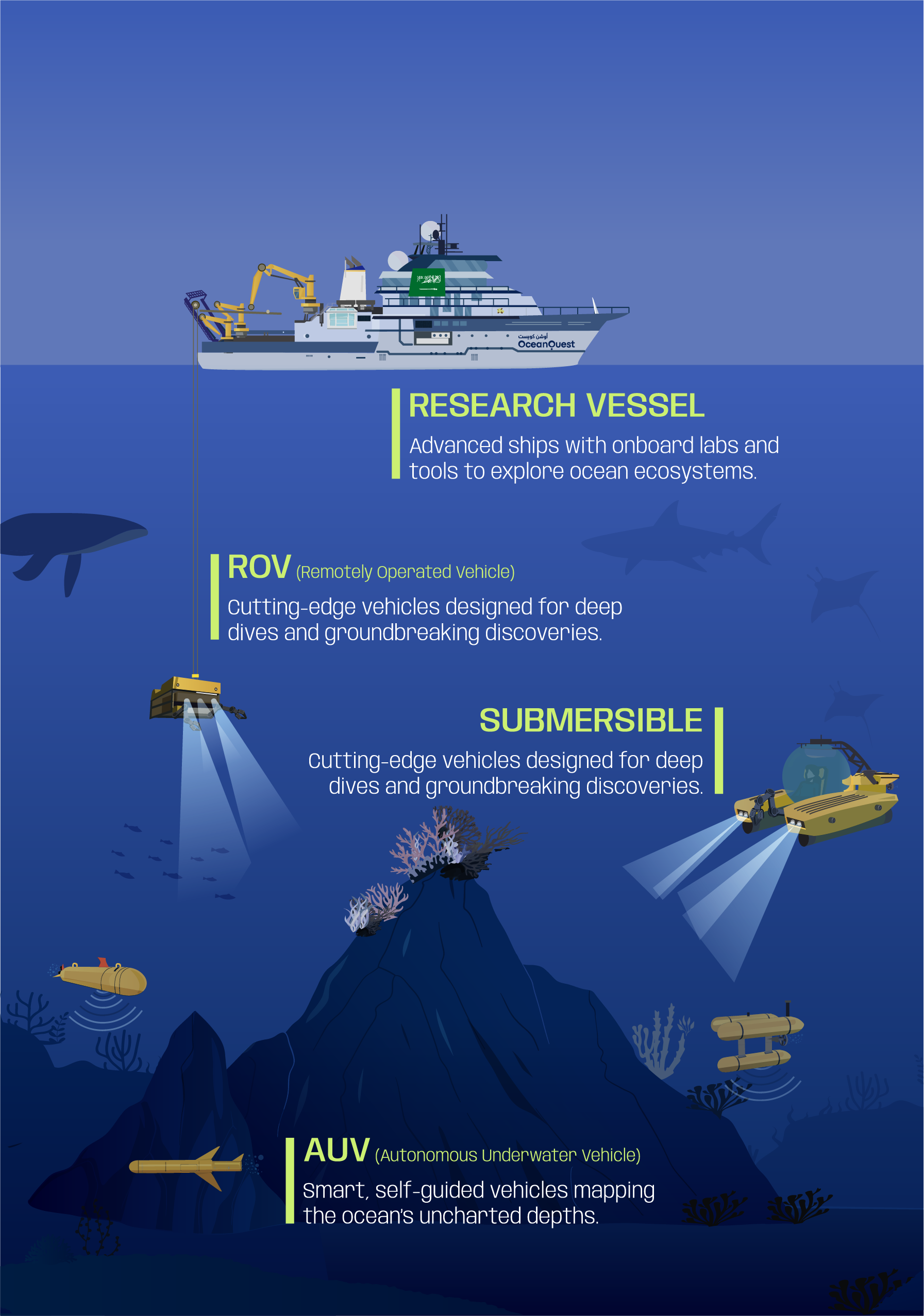
Deep Ocean Exploration Technology
Files labeled as "Private Combolist Cleaned.txt" are frequently used as bait. Users looking to download these lists often find themselves downloading "stealers" or "Trojans" instead, turning the would-be attacker into the victim.
While the search for a "Private Combolist Cleaned .txt" might seem like a shortcut to digital power, it is a hallmark of the cycle of cybercrime. For the average user, the existence of these lists is a reminder of the importance of unique passwords and robust security settings. For the industry, it is a call to move beyond the traditional password toward more secure, biometric, or token-based authentication.
The phrase refers to a specific type of file often sought after in cybersecurity circles and, more frequently, the "underground" web. To understand why this topic is significant, one must look at the mechanics of data breaches, the ethics of credential stuffing, and the ongoing battle for digital security. What is a Combolist?
From a cybersecurity standpoint, combolists are a valuable tool for defense. Security researchers and services like Have I Been Pwned use these lists to alert the public. By analyzing which passwords appear most frequently in "cleaned" lists, experts can develop better encryption methods and advocate for . Conclusion